What is HackenProof?
HackenProof is the cybersecurity vendor providing security testing services to clients representing such industries as blockchain, information technologies, retail, financials, etc. HackenProof is also one of the leading professional bug bounty platforms uniting 5K+ white hat hackers worldwide. The project operates as a part of the Hacken ecosystem of cybersecurity products. HackenProof is trusted by both emerging projects and reputable brands and the services offered by its specialists are also demanded by the entities from the public sector. For more information about HackenProof, its clients, achievements, and cooperation details, please view the following article.
What is a bug bounty program?
Bug bounty program is the form of security testing that allows companies to invite independent ethical researchers to work on identifying vulnerabilities in their products and systems under the specified framework. Independent researchers get rewards for detected vulnerabilities and the size of these rewards is determined by companies before the official launch of a bug bounty program. Often companies apply for running bug bounty programs on professional platforms in parallel with conducting other forms of security testing including penetration testing. Bug bounty programs allow companies to avoid spending huge resources on employing large internal cybersecurity teams and, generally, they have become a must-have security process for most reputable technological brands.
Bug bounty program & end-to-end encryption
End-to-end encryption is the technology making transmitted data such as files or messages accessible only to the specified recipients. The transmitted data becomes unreadable for law enforcement agencies, providers, app developers, and malicious actors unless they have a decryption key. End-to-end encryption is a highly effective instrument for companies striving to prevent data breaches that may result in the compromise of customers’ sensitive data such as banking credentials, credit card details, contact information, etc. The use of end-to-end encryption increases the chances for companies to be compliant with strict data protection regulations. End-to-end encryption guarantees almost 100% protection of the data being transmitted but as soon as the information reaches a recipient, it becomes vulnerable to breaches unless adequate security measures are in place.
Under the PCI DSS Requirement 3, companies are obliged to avoid sending PAN (primary account number) in unencrypted messages and are strongly recommended to encrypt every piece of information they need to store. However, end-to-end encryption is just one of the measures companies should take to become PCI DSS compliant. The use of bug bounty programs allows companies to identify weaknesses the exploitation of which may allow attackers to access sensitive data and files located in companies’ storage.
Bug bounty program & PCI DSS compliance audit
To become PCI DSS compliant, the entities processing debit/credit card payments have to achieve 6 separate goals – PCI Security Standards. For example, entities need to regularly test security systems and processes, protect stored cardholder data, and restrict access to cardholder data. The bug bounty program is the security testing mechanism by passing which on regular basis companies can meet some of the key PCI Security Standards. Also, bug bounty programs may allow companies to detect issues in their access control systems, networks, and security policy. To become PCI DSS compliant companies need to prove their ability to prevent data breaches and bug bounty programs are the measures that allow companies to identify and eliminate the channels through which malicious actors can get access to and steal the sensitive data stored by entities.
How much can you save by running bug bounty programs?
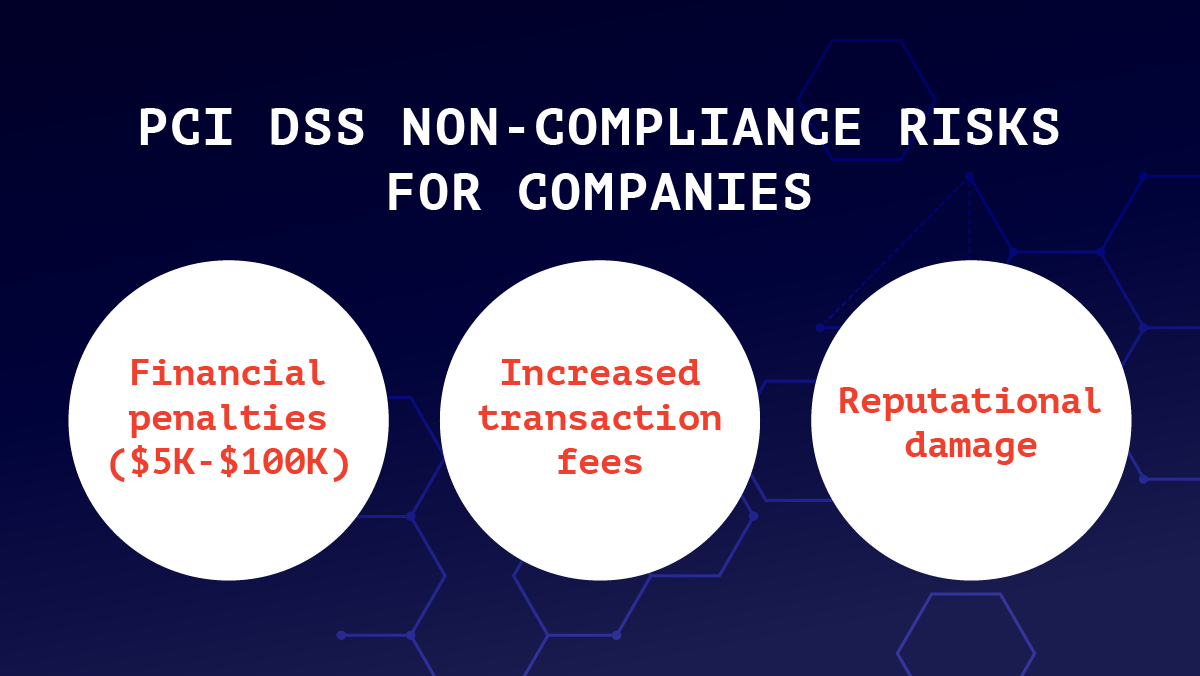
When companies fail to comply with the PCI DSS standards they have to pay fines to the payment processor with whom they have signed a contract. The higher the volumes of transactions the company processes, the higher the fines it may face for PCI DSS non-compliance. Payment brands impose fines on acquiring banks and the latter, in their turn, pass these fines to merchants. The fine may range between $5K and $100K per month. Also, when companies fail to comply with PCI DSS standards, their respective banks may increase transaction fees or even terminate cooperation with these vendors. For SMEs, these penalties may be catastrophic while for large companies PCI DSS non-compliance may result in huge reputational losses.
How much do you need to spend on a bug bounty program?
The cost of running a bug bounty program on professional platforms includes the fixed subscription fee set up by the vendor organizing such programs and the rewards paid by companies to ethical hackers for revealed vulnerabilities the amount of which is determined by companies themselves. For a better understanding of the bug bounty program pricing scheme, you may view the subscription plans offered by one of the leading bug bounty platforms HackenProof. At the same time, the amount of reward paid by companies to independent researchers may range between a few hundred USD and a few thousand USD or even much more depending on the severity of revealed vulnerabilities. However, when comparing these figures with the sum of potential penalties companies may face for PCI DSS non-compliance, then it is reasonable to conclude that investments in cybersecurity bring high ROI.

