Twilio: are there any security risks involved?
Twilio is the customer engagement platform used by developers to build the desired customer experience through such capabilities as WhatsApp, SMS, email, voice, video, and even IoT. Twilio powers communication for 190,000+ businesses thereby enabling close to 932 billion human interactions per year. As of 2021, more than 9 million developers worldwide use Twilio for professional purposes. Developers build applications using Twilio APIs while the platform is responsible for managing connections between the Internet and global telecommunications network.
Generally, Twilio is functioning under the Communication Platform as a service (CPaaS) model. Twilio allows app developers to reduce the financial and time expenditures required to develop an app. Twilio offers its clients top-notch security and high-quality performance.
At the same time, developers of the companies using the platform are responsible for the final configuration of solutions provided by Twilio. There is the risk that due to mistakes or improper setup developers may leave vulnerable points that may be exploited by hackers. Although the platform strongly recommends its users to use HTTP Authentication together with encryption to secure communication between the application and Twilio as well as add validation to prevent interacting with malicious third party services, companies may lack expertise and understanding of how to correctly apply these security measures. That is why companies building their solutions on Twilio should not rely solely on the security practices followed by the platform but also apply for independent security testing such as bug bounty programs to identify whether their communication with clients is secure enough to prevent the theft of private information or even commercial secrets.
Running a bug bounty program: what value do you get?
A bug bounty program is a form of security testing whereby a company delegates to independent ethical researchers the identification of vulnerabilities in its products and pays rewards to them for reports on these issues and the instructions on how to address them. One of the key advantages of a bug bounty program compared to other types of security testing is the principle under which a client pays only for the detected bugs and the list of bugs that should be reported to a client is specified in the official rules of the program. Independent researchers participating in a bug bounty program can apply advanced methods and techniques to estimate the security of a product under test and their skills and knowledge, in most cases, go beyond the expertise of the internal cybersecurity specialists of a client. Generally, by running a bug bounty program companies can effectively test the security of their products and eliminate vulnerabilities within a prescribed timeframe.
Benefits of running a bug bounty program on professional platforms
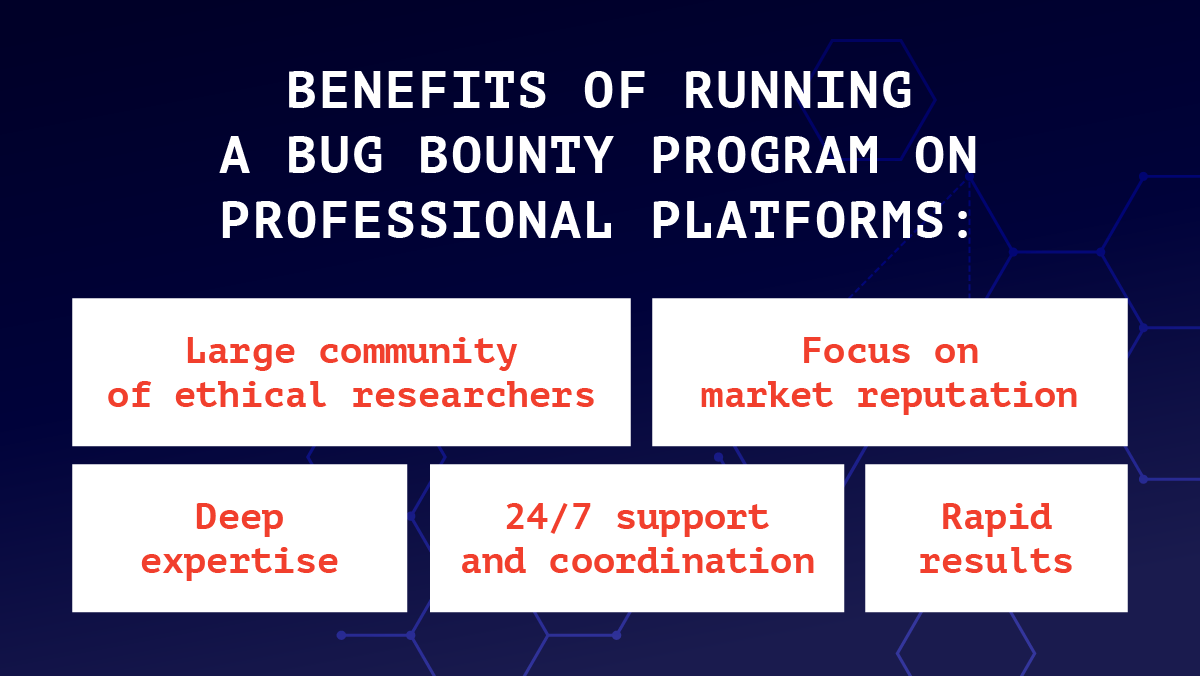
Companies are free to decide whether to organize their own bug bounty programs or apply for services provided by professional vendors like HackenProof. When organizing their own bug bounty programs companies are fully responsible for the development of rules and terms and the activities performed by the invited researchers. Also, most companies do not have a large community of external researchers who can immediately start working on detecting bugs in their products.
On the contrary, professional platforms have large communities of independent ethical researchers whose professionalism is proven by the previously demonstrated results and who are highly motivated to follow ethical standards to avoid being banned from participating in other programs organized by a vendor. Also, the larger the community of ethical researchers, the higher the chance that many specialists are ready to start working on a program immediately. That is why by applying for running a bug bounty program on professional platforms like HackenProof companies can get high-quality outcomes under the given period and the risks that their systems may be damaged due to unethical behaviour of researchers is minimal.
Why HackenProof?
HackenProof is one of the leading European bug bounty platforms that has been addressing security issues affecting clients’ products since 2017. The project is functioning within the Hacken ecosystem of products. Our community of ethical researchers unites 5,500+ specialists who have already detected 900+ bugs in clients’ products. HackenProof is trusted by companies representing both private and public sectors. Currently, our services are highly demanded by the projects from the crypto industry where security risks are the highest due to the volume of circulating assets. It’s the indicator of our strong status and reputation. Our independent researchers are aware of the advanced techniques and hacking methods used by hackers and they know for sure how to prevent black hackers from reaching their goals.
Compared to other vendors, HackenProof offers highly attractive subscription plans to its clients. Also, we are fully transparent in our pricing methodology. There are no hidden fees or other expenditures.
How to apply for running a bug bounty program on HackenProof?
You just need to contact our team through the chatbot on our website or reach us on social media. Our specialists will instruct you on the next basic steps required to launch a program.
HackenProof Facebook: https://www.facebook.com/hackenproof/
HackenProof Twitter: https://twitter.com/hackenproof
HackenProof Telegram: https://t.me/hackenproof
HackenProof Instagram: https://www.instagram.com/hackenproof/

