On December 12th, we identified an unprotected MongoDB instance which appeared to be part of ESET’s cloud infrastructure. An IP with a default MongoDB port was indexed by IoT search engine Shodan and was available for anybody to view, access and edit.
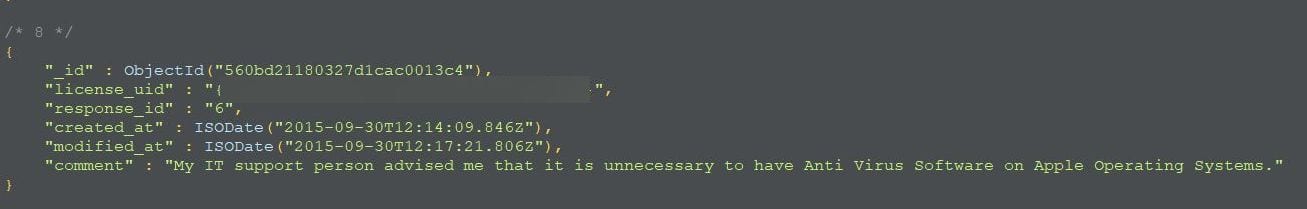
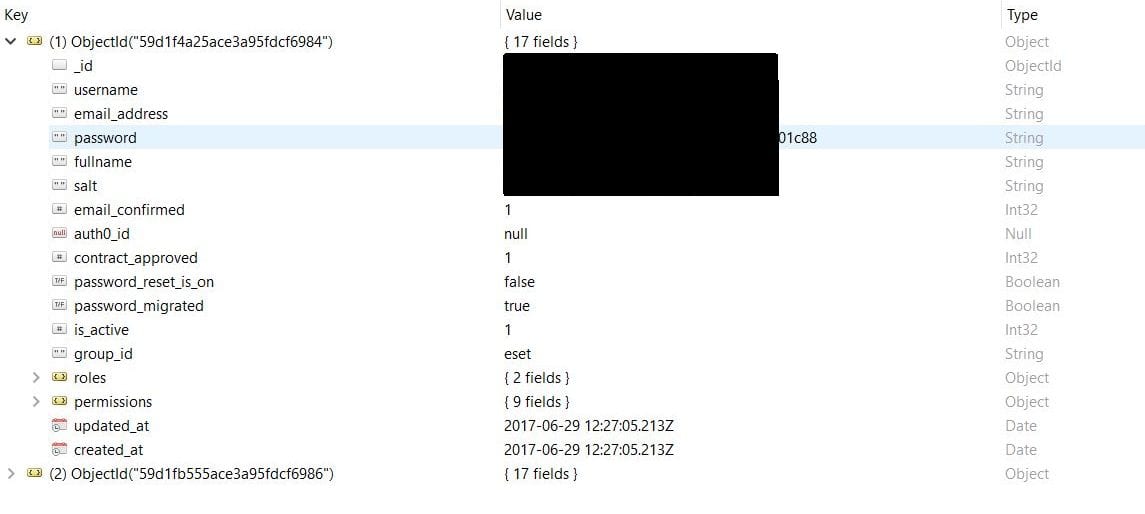
A 50GB database contained information relating to ESET’s products distributed by South Africa’s division, i.e. licenses order purchase info, including owners’ names, license keys, license passwords, emails, license files – more than 12 thousands files. Additionally, the database contained a list of email addresses (blacklist, greylist, whitelist), customers support feedback, plus two administrator usernames and login details (hashed and salted passwords).
Upon discovery of the misconfigured database we immediately sent a security alert notification to the ESET security team and on December 17th the instance was taken offline. The ESET team has acknowledged the incident and has provided us with the following statement:
ESET’s Security team would like to thank Bob Diachenko for responsibly reporting the vulnerability to us. This information has helped us to improve the security of our online services while preventing malicious exploitation of this vulnerability.
We have already reported on the dangers of inadvertent exposure of MongoDB instances due to the numerous attacks by hackers, with malicious intent, who access the unprotected databases. The hackers delete data and leave ransom notes demanding bitcoin in return for restoring the system to its original state. Fortunately, we discovered the problem and enabled ESET’s database to remain intact t thereby preventing ESET’s customers from being affected.
The main takeaway from this is how important security is at every stage of the development process.
There is no doubt that your development network must be one of your most secure networks for it contains your intellectual property. The ESET incident has taught us that transient firewall rules may inadvertently expose your development machines to the public. However, in this case, it appears to have only exposed a limited amount of personal information, but in other cases, it could be that critical intellectual property or even your entire subscriber base that could be exposed.
To learn how engaging with the global community of independent security researchers can reinforce your network security, you can sign up for a free trial demo, and our experts will be in touch with you shortly.

